Make your digital signatures legally-binding!
Achieving Legal Certainty on a Global Scale
If you are planning to use electronic signatures, more than likely you will want your signed documents to be legally binding – otherwise there would not be much point in signing them in the first place!
Although all types of e-signatures can be potentially submitted as evidence in a court of law, only the more advanced types which give greater assurance of the signer’s identity and document authenticity, will carry the necessary evidential weight to be upheld in a court and be granted functional equivalence to a hand-written signature.
FAQs
The statutory requirements for an electronic signature vary slightly among the different e-Signature Laws around the world (e.g. US E-Sign Act and EU eIDAS Regulations) but are essentially equivalent and boil down to a few key areas. So if you are implementing electronic signatures in your organisation and want to have legal certainty then ensure you ask the following questions:
Does the signature identify the signer?
This most basic requirement is that the signature should identify the signer by name and if appropriate additional attributes such as their position within a company.
SigningHub uses unique digital certificates (X.509 digital identities) for each signer and these are embedded within each signature that the user creates, hence it’s easy to establish who signed a document. The issuer of these digital certificates can be externally trusted identity providers e.g. governments, financial institutes, Qualified Certificate Authorities, Internet Certificate Authorities etc. and SigningHub can act directly as the certificate issuer as well. Different business applications and jurisdictions will have different requirements on which identity providers are trusted. It’s important that a signing solution can work multiple Certificate Authorities (CAs) and identity providers to allow easy configuration of trust points required by enterprise or specific department.
If your e-signing solution provider is not using individual digital certificates for each signer, then the signer’s digital identity is not cryptographically linked to their signed documents and therefore such documents will not be verifiable independently of your service provider.
Can the user make their signature mark on the document?
Just like an ink signature on paper, an e-signature user should still be able to make their mark on a document to indicate their consent. This needs to still be recognisable to humans as a signature mark.
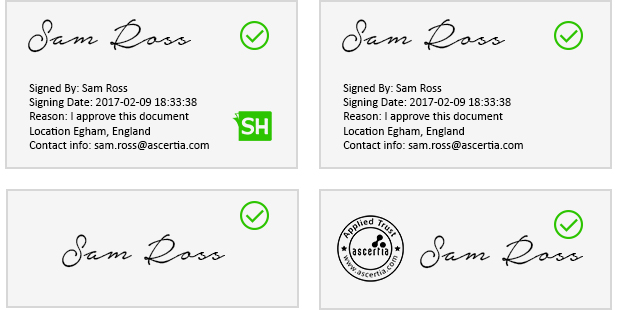
SigningHub allows the user’s hand-signature to be captured through various means like drawing on touchscreens, using scanned images, special text-font signatures or drawing on specialist hardware-based signature tablets. This hand-signature together with various meta-information like the signer’s name, reason for signing, date/time of signing and contact info, plus company logos can be stamped as the user’s mark on the document. SigningHub provides the capability to design the signature appearance to suit your needs:
Can the signer’s intention to sign be proven?
The overall signing process should be designed to minimize the risk that signers could legitimately claim later that they applied an electronic signature without realizing its legal significance – i.e. without understanding the reason for signing and/or without an intent to actually sign.
SigningHub allows a clear and conspicuous legal notice to be shown that a signature is being created and that it will be legally binding. Administrators can pre-configure such legal notices and easily assign to documents within workflow templates.
Furthermore the signer can be forced to select a reason for signing from a pre-configured list, as well as requesting their initials on each page or against important paragraphs. This all goes a long way in proving that the signature was created as a wilful act and not by mistake or without understanding the legal implications of signing the document.
Can you prove the signer was the only one who could have created the signature?
The electronic signature should be created using a private signing key under the sole control of the signer. The same signing key must not be shared with multiple users or be available to service administrators. This prevents the signer from claiming someone else created their signature.
SigningHub uses unique digital signature keys for every user – a major difference from our competitors. These signing keys can be held on PIN-protected smartcards/secure USB tokens /mobile devices – so under the sole control of their owner. Alternatively each user’s unique signing key can be held securely on SigningHub servers in encrypted form and only released for signing after strong identification & authentication and authorisation by the user who owns the key.
Can the signature be verified many years into the future?
Important documents may require verification months and years after signing. The legal certainty of the signature verification process must not be eroded over time. It should be possible to extend the lifetime of signatures beyond current state-of-the-art cryptographic algorithms.
SigningHub creates advanced long-term signatures which include embedded timestamps to prove the time of signing and proof that the signer’s digital identity and signing key were valid at the time of signing. Furthermore SigningHub’s be adherence to advanced standards (e.g. PAdES Part 4 and XAdES-A) ensure the signature lifetime can be automatically extended over time by embedding a fresh chain of trusted timestamps.
Can the signature be verified independently of the solution provider?
The signature should be in a standard format so that it is verifiable in 3rd party software, without requiring documents to be uploaded or sent to the service provider.
This is essential for the longevity of your signed documents. You may change signature solution providers in future or your current provider may cease trading. It’s important you retain your signed documents and can verify them independently of the solution provider. There should be no lock-in. SigningHub follows exactly these principles and is dedicated to industry standards for user identification & authentication and document signing.
Is there a complete audit trail?
The signing solution provider should keep a complete audit trail of each signing action as supplementary evidence. The primary evidence is the digital signature itself.
SigningHub retains full and detailed logs of all actions performed on a document. Each action is date/timestamped, together with details of who performed the action, and related meta-information about the event (e.g. IP address, type of device used and low-level details of the action). If required, screenshots and recordings of the signing can be captured as well for additional proof of signing.