Why SigningHub is the most secure way to sign
Supports All Signature Types
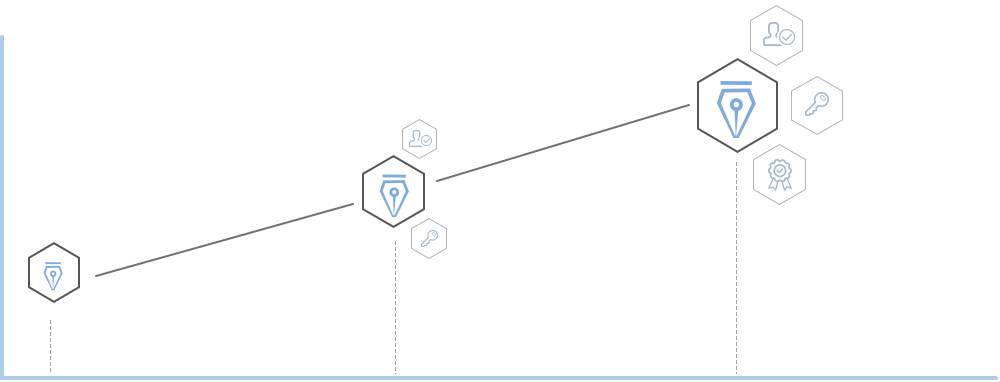
Basic
Immediate signing, no user registration or login required
Document protected with server e-Seal
Advanced
Uses unique PKI signing key per user
Strong user authentication, user identity cryptographically-bound with signature
Strong non-repudiation
Qualified
Highest level of legal recognition & acceptance
Cross-border use under EU eIDAS Regulation
Relies on Gov-recognised CAs only
Supports All Signature Types

Basic
Immediate signing, no user registration or login required
Document protected with server e-Seal

Advance
Uses unique PKI signing key per user
Strong user authentication, user identity cryptographically-bound with signature
Strong non-repudiation
Qualified
Highest level of legal recognition & acceptance
Cross-border use under EU eIDAS Regulation
Relies on Gov-recognised CAs only

Adobe® AATL Signatures
Get automatic recognition and wide acceptance of your signed PDF documents globally by relying on high-trust AATL signatures

Adobe® AATL Signatures
Get automatic recognition and wide acceptance of your signed PDF documents globally by relying on high-trust AATL signatures

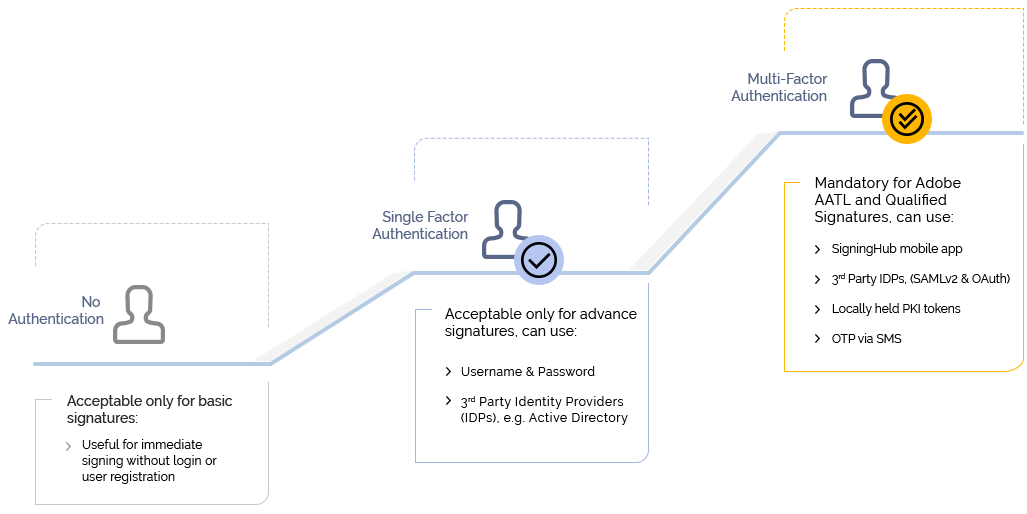
Configurable User Authentication
SigningHub supports many different user authentication options so you can tailor to your business need, ranging from no authentication to very secure multi-factor authentication. Which option is used depends on the user’s service plan and/or the type of signature being created.

Long-Term Validation (LTV) enabled
SigningHub creates signatures which are verifiable in the long-term, i.e. 10, 15 or 20+ years. To achieve this requires strong cryptographic security and adherence to LTV signature standards.

Long-Term Validation (LTV) enabled
SigningHub creates signatures which are verifiable in the long-term, i.e. 10, 15 or 20+ years. To achieve this requires strong cryptographic security and adherence to LTV signature standards.

Configurable Trust Anchors
With SigningHub you can choose which Certificate Authorities are trusted to issue digital identities within your custom service plan
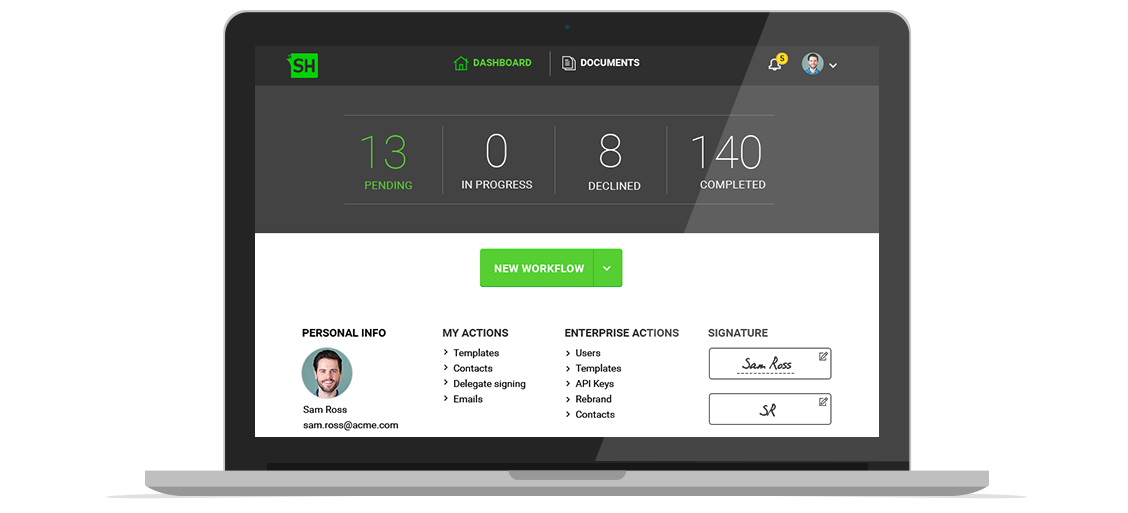
Enterprise Management Control
Invite users, manage roles, configure your branding and control default settings from the enterprise dashboard

Document Access Control
Prevent Man-in-the-Middle (MITM) attacks and control access rights on a per recipient basis

Strong Crypto
SigningHub uses latest security protocols, crypto algorithms and key lengths

Certifications & Compliance
Whether on-premise or in the cloud SigningHub complies with a range of certifications. Qualified TSP hosting partners are also available
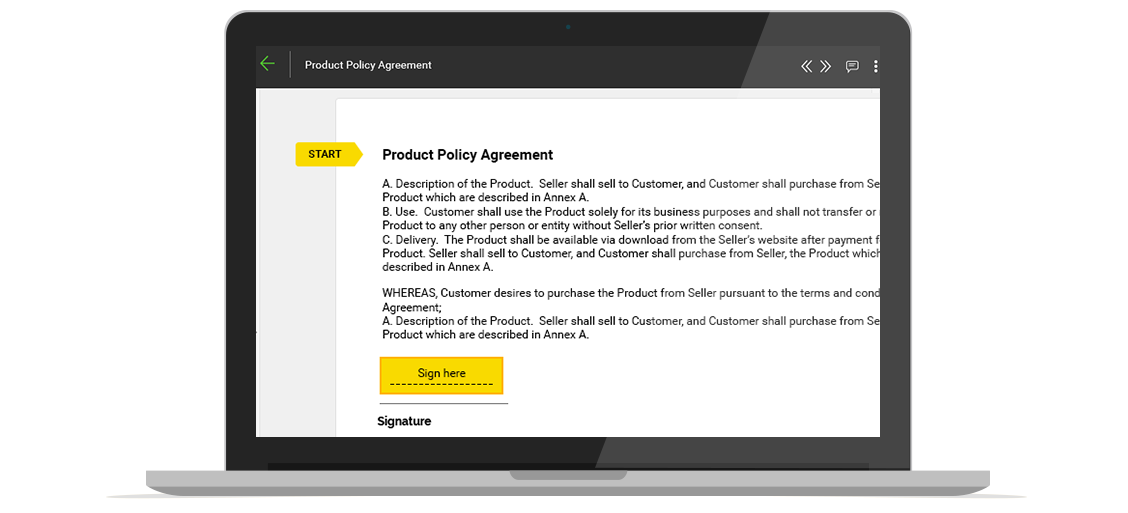
Secure Document Viewer
It’s essential that users can clearly review what they are about to sign & approve, referred to as “What You See Is What You Sign” (WYSIWYS). SigningHub comes with its own built-in secure document viewer

With your help, over 5+ years we have been on an excellent journey from a simple PKI solution to a robust SigningHub platform

Jude Pereira
Managing Director, Nanjgel Solutions
With your help, over 5+ years we have been on an excellent journey from a simple PKI solution to a robust SigningHub platform

Jude Pereira
Managing Director, Nanjgel Solutions